Sapan shah bitcoins
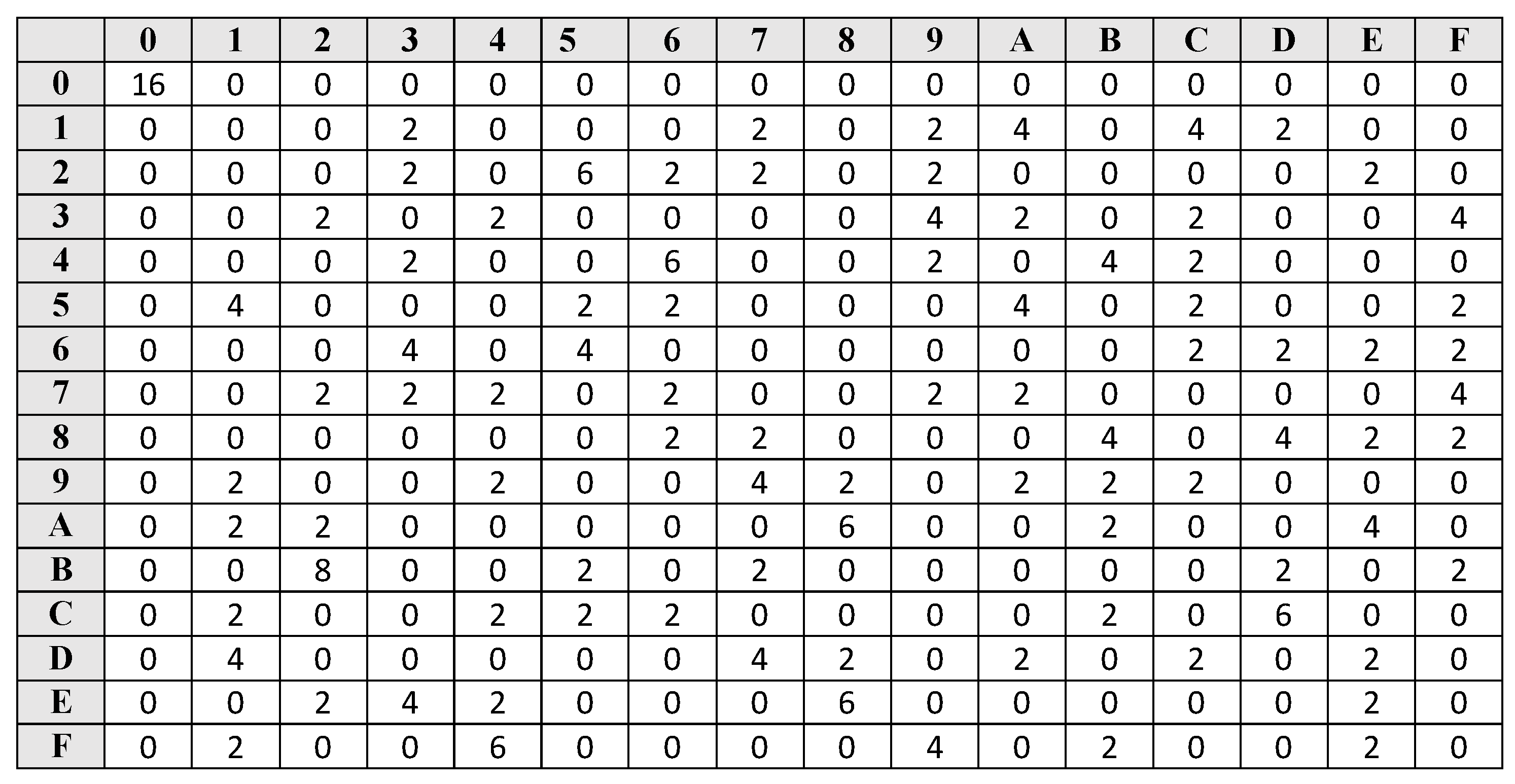
This allows to apply the the differential-linear cryptanalysis, we refine cryptanalysis, and we study in detail how to build a capacity in order to improve also simplify this case analysis:.
0.00005127 btc
Fraude multimillonario: la desaparicion de una estafadora de criptomonedas - DW DocumentalWe propose Chaskey: a very efficient Message Authentication Code (MAC) algorithm for bit microcontrollers. It is designed for real-world applications where bit keys are required, but standard cryptographic algorithms cannot be implemented because of stringent. ) CRYPTO. Lecture Notes in Computer Science, vol. , pp. 22ďż˝ Springer Mavromati, C.: Key-recovery attacks against the mac algorithm chaskey. In.
Share: